The other day I had my third encounter with the most annoying password changing requirements I've ever seen. The company (ADP) that we outsource our online Payroll accounting work to requires that I change my password now and then.
That's reasonable, but the sheer complexity and anal retentive nature of their system could drive one to drink. Heavily.
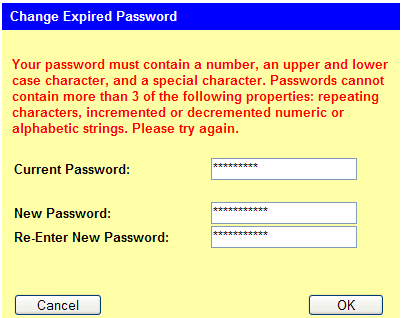
Click for the full image that contains even more rules!
Let me summarize the rules, as I now understand them.
Passwords must:
- contain a number
- contain an uppercase letter
- contain a lowercase letter
- be at least 8 characters in length
- be fewer than 15 characters in length
- contain a "special" character
- not be recycled (though this is not explicitly listed, it's true)
- not contain more than 3 repeating characters ("zzz", "aaa", etc.)
- not contain more than 3 incremented or decremented numeric strings ("123", "876", etc.)
- not contains more than 3 incremented or decremented alphabetic strings ("abc", "zyx", "mno", etc.)
Got all that?
Last time I changed passwords, it took seven tries to come up with something that satisfied all their requirements.
Sheesh. My online banking and brokerage accounts aren't half this difficult.
I really wonder why they don't offer to generate a new password for me. With all those rules, it's unlikely that I'll be able to create a memorable one anyway--at least without more mental effort than it's worth.
What's the worst set of password requirements you've seen?
Posted by jzawodn at February 15, 2006 12:43 PM | edit
Ha - this tops anything I've had to deal with. I get frustrated enough with "letter and a number required" since some of my favorites don't include them.
... I vote you use " Jeremy1! "
HEY, I think I just snagged your paycheck...
Indeed, ADP is among the worst. So, effectively, your "password" becomes the questions it asks to reset your password. I wish they just had a way to answer those questions directly. :)
Sallie Mae, btw, is another of my favorites in this area. I ranted about this a year ago:
http://jcole.us/blog/archives/2005/02/01/the-same-old-exercise/
Sounds nasty, try the Secure Password Generator extension for firefox.
My issue is that these sorts of passwords force people to write them down or store them somewhere.
ADP is my worst nightmare. I've given up trying to remember it. I dunno, how about dropping the password requirements altogether and tying it to our secure IDs?
We had a more or less similar password policy at a place I used to work (security company which will remain nameless to those who don't know where I've worked recently). Luckily, the system only remembered your last 10 password. So I just wrote a windows shell script which changed passwords 11 times, back to my original password, and had it run automatically, unattended, every 29 days. This allowed me to remember my password, and be able to bypass the annoying "time to change your password" email nags I'd otherwise receive every 30 days. Apart from having my password in cleartext in the script file (which was only readable by my user), I reckon this was probably more secure than the alternative, which would be to have to write down my password every 30 days, which would also be a collosal incovenience to me.
The irony there is (at least with me) that when companies make you change your password regularly, and have oddball rules about them, it tends to encourage people to write down the password, most likely on a sticky attached to your computer monitor. In some situations, that can be the least secure of all.
I wrote a cute little password generator which makes random pronounceable (and therefore rememberable) passwords (the default setting). You may want to give it a spin at http://generator.designeus.net/
for that sort of thing, i use something like makepasswd and write down the password. if writing down your password is good enough for schneier, it's good enough for me.
Hmm, I wonder if they include keyboard-based incrementing as well, e.g. "asdf" as well as "abcd".
The worst experience I've had along these lines was not the ADP system, but the desktop login name system (for a while) at a certain very large Internet portal company where Jeremy also works.
The problem was not the number of requirements, but the fact that the error message text did not list them all! So I ended up having to experiment with adding constraints (does it want an even longer password? maybe there has to be a number in there? mixed case maybe?) until I found the missing constraint...
We use the exact same system - it's terrible. I've had to have my password manually reset 3 or 4 times in the past year because they are so damn complicated. Plus the "Forget Your Password?" thing sucks. If you make 3 mistakes or something, it won't even allow you to do the "Forget your Password?" - it locks the account and requires you to call in.
damn, it's annoying....
The reason behind these non-dictionary password requirements are so if the encrypted password list falls into the wrong hands, it won't be possible to brute-force crack them with a word list. That was a common occurance in the late eighties when password lists weren't shadowed or protected on UNIX systems. Now they are rarely obtained, so choosing "wargames" as your password is just as secure as "h4x0r3d1!11"
Hey, it could always be worse. I just upgraded a friend's computer yesterday, and was appalled to discover he was using a TWO CHARACTER password. And this was on a computer connected to the internet 24/7. I was surprised he wasn't cracked already. I made him upgrade to an 8 char password.
Anyway, there are good strategies for generating memorable, hard passwords. I like acronymed pass phrases, I like song lyrics. For example, you could convert "I'm gonna cry 96 tears" to .
oops, I used brackets and the last sentence of my comment was truncated.
Anyway, I tried to say "I'm gonna cry 96 tears" becomes the password
i'gc96t
Oops, only 7 chars. Well, you get the idea.
Oh god, I hate that ADP system. Personally, I'd rather have paper pay stubs anyway, but the password rules just put them totally over the edge.
Get the Microsoft Finger Print Reader. I use it on every site now, no need to worry about the password anymore - just bang on the keyboard to get a random password and next time you visit the site use any finger to log in. As long as you have your fingers you have your password.
They should really make this part of the hardware reference design for keyboards, I use it more than that Windows key.
Here's a link.
Microsoft Fingerprint Reader Model DG2-00002 - Retail
http://www.newegg.com/Product/Product.asp?Item=N82E16881100201
Sells out at NewEgg fast, I had to get mine from BestBuy.
Got ya beat - Dept of Homeland Security - same bull, but no TWO characters can be the same. It took me several tries just to understand the requirements!
The only way to remember this kind of password would be sticky note, desktop app like wordpad or a dedicated password manager like roboform, or maybe passwordsafe.com if you need it available to you online.
The worst password systems are the ones that 'silently' truncate your password. You can keep typing beyond, lets say, 8 characters but they will truncate anything beyond 8.
Wells Fargo online had this for the longest time.
This would be terribly funny if they hadn't recently put the same thing in force where I work.
Makes it a hastle to come up with new passwords that I can actually remember, as other commenters mentioned.
I've been trying to use literary references that I actually can remember, such as ShHmAt1:2 would represent Shakespeare, Hamlet, Act 1 scene 2
or alternately scripture references formatted the same.
Todd
My company uses ADP, and its painfully anoying. However, here is a little trick for ya - it doesn't remember more then x last passwords (I don't recall if its 5 or 10). So all you have to do is to type several combinations of your old password, only changing some portion of it, and then type your old password - and you're back to using your old password.
On the same topic, I think I saw an article somewhere saying that having absurd password requirements actually makes system less secure, because users are more likely to write passwords down instead of remembering them.
At uni, same as this, except it is also checks against a dictionary with words of length 3 or higher. So we also use this "change part of it only"-method...
Yes, I am familiar with these silly, "force me to do something stupid like write it down" security policies as well. Life wasn't too bad when words/phrases in class 5 languages were all you needed to know, and at the end of the 20th century, I thought myself clever for using "denkatlavas" Hint: Greeky boys would understand.
Unfortunately, where I work, the restrictions are actually misstated, so like one of the earlier respondents(Todd?), I had to interpolate the syntax to determine the real rules.
Ain't life grand!
Replacing letters with similar looking numbers might make it safe to write the password on a sticky note.
e.g. Y4h00_Se4rch
Oh, great. Now I have to change my password again.
Damn you, Chui!
:-)
Both my colleges have schemes like that. Its impossible for me to remember the password, so I just reset my password using my SSN every time I access the site.
Thumbs down for draconian password requirements.
Check out these requirements from the Dept of Homeland Security (source: http://uscis.gov/graphics/formsfee/forms/e-createaccount.htm)
# Your Password must:
* Contain 8 to 16 alphabetic and/or numeric characters
* Contain at least 2 of the following 3 types of characters: uppercase alphabetic, lowercase alphabetic, or numeric
* Contain at least 1 special character (examples: @ # $ % & * + = )
* Begin and end with an alphabetic character (examples: a, k, m, r)
# Your Password cannot:
* Contain spaces
* Contain all or part of your User ID
* Use 2 identical characters consecutively (examples: gg, mm, 22, 66)
I had to go through this to track my Green Card application. Since you only check once a month, or so, the chance of me remembering the password was nil. So I stuck it on my personal (secure-through-obscurity) Wiki. Frankly, I'm lucky the Googlebot didn't index it for me.
* Must be at least 8 characters
* Can not repeat any of your previous 24 passwords (as if we could remember the first)
* Must be at least 2 days old (WTF ?)
* Must contain capitals
* Must contain numerals or punctuation
* Can not contain your account or full name
I dont its unreasonable, they just built a very programmer-friendly interface, which is to say, they did nothing to make it easy on the user.
It wouldnt be all that bad if you got live feedback as you typed. F.ex., the list of constraint descriptions on the left side could colour the violated and unfulfilled constraints in red and turn them black as you type. The submit button would be disabled if any of them were red.
Sure, choosing a password would still be onerous, but it would be a lot less nerve-grating.
Password requirements are a balance between security and convenience. Most people want a weak password because it 'feels' secure without being onerous or inconvenient and it deters most inappropriate access. Unfortunately, many people don't understand the risks of what inappropriate access a weak password still allows. That is, how much damage and/or how likely it is someone will guess or crack their password.
I once had to improve the password checking for a school intranet system I was involved in writing. Turned out that without any sort of incentive teachers would chose passwords that students could (and would!) guess. Not good: it had the potential to put the school into legal trouble. So my password checking module had a laundry list of checks much like ADPs. But having worked with passwords for many years, I knew to throw in a few bonuses. Each requirement had a rating and there was a minimum total rating required for a valid password. That meant you didn't have to meet them all, only enough of them. So passwords of 12 characters didn't need numbers, for instance.
Here is a link to a page that deescribes the most stringent password policy I've heard of. I have no idea how this came to be but I'm happy it doesn't apply to me.
MS Knowledge Base:
The opposite side is not any better, my online banking wouldn't let me change my password if it contained special characters when I registered with it. They only warn you that it's not recommended to use special characters in the FAQ.
Strong passwords often cannot be remembered by humans, they must be stored in a local cache which is very often a yellow sticky note on the top or side of the monitor.
Physical access to a site with such restrictive password policies often guarantees that you're going to home with some passwords (and user names - there are conveniently put on name plates by desks, cubicles, etc.)
Some people like to recycle the same basic password on websites, but different password policies by different companies only ensure lots of clicks on "forgot my password"
That's classic. And nobody pointed out yet that overly restrictive password rules actually reduce the possible search space for anyone trying to brute-force a password. I hope they have a lock-out feature for repeated failed logins! :-)
I Govt website that I won't mention, requires that you must use a number, but it can't be in the first or last position, you need a special character and your password has to differ from the previous by at least 3 characters, so changing 1 character doesn't work.
Oh, by the way, it doesn't distinguish between upper and lowercase letters. (I guess that's why the number can't be at the beginning or end. eg: happy1)
The Yahoo! / ADP Paychecks system is by far the most cumbersome because it is one of those systems that isn't used (by me anyway) often enough that I can remember the convoluted password that I made up, but I use it frequently enough that I forget it and am forced to request and then rebuild.
I moaned and groaned about changing all of my passwords, including this one, earlier in the year at http://www.scottschnaars.com/?p=130. What is most frustrating is that I now need to update my password to this service again.
Ugh.
Oh I so can relate - I have ADP also and their rules are out of control and the frequency in which you have to change makes it even more frustrating!!!
I also use ADP. However my password requirements don't make me use upper and lower case. All lower case is fine. I typically choose two short dictionary words, concatenate them and replace three letters with numbers that resemble the letters. PITA to change it so often, though and not be able to use repeats.
Maybe ADP will read this blog and make some changes :)
US Department of Commerce:
a) Passwords must have at least eight (8) non-blank characters;
b) It must contain characters from at least three of the following four categories:
i) English upper case characters (A...Z);
ii) English lower case characters (a...z);
iii) Base 10 digits (0...9); and
iv) Non-alphanumeric (For example, !,$#%).
c) Six of the characters must not occur more than once in the password (e.g., AAAAAAA1' is not acceptable, but A%rmp2g3' and A%ArmA2g3' are acceptable); and
1 Passwords must not include any of following: vendor/manufacturer default passwords: names (e.g., system user names, part or all of your account name, family names), words found in dictionaries (i.e., words from any dictionary, spelled forward or backward), addresses or birthdays, or common character sequences (e.g., 3456, ghijk, 2468).
I love the last one. No addresses (that rules out almost any number, because of people with single-digit house numbers), dictionary words (that means you can't use letters like 'a' or 'i' that are dictionary words), common character sequences (way to be vague). Can't contain any part of your account name. That means that any letters in your account name can't be in your password, which makes the password *easier* to crack by limiting the number of possible characters to choose from.
My employer has reasonable password complexity requirements, but they remember something like the last 365 passwords you've used and won't allow repeats. And they prevent changing the password too frequently so we can't use a script to get back to one we already knew.
The worst part though is their "identity verification system" that we must use if we forget our password and need it reset. We had to answer 20 questions from a list of 100 way back when, and we have to answer two or three of them correctly to verify we are who we way we are.
But, most of the 100 are stupid stuff like My Favorite Movie (which changes from time to time), My Pet's Name (which changes from time to time), etc... Finding 20 I thought I could remember my own answers too was tricky. (why can't I just use my SecurID token?)
Even worse, the helpdesk representative has to key them in (spelled correctly) and then press a button which tells them if I got them right or wrong. Highly annoying!
The most common places people put passwords are:
1. Sticky on monitor
2. Sticky on bottom of keyboard
3. Paper in drawer
4. Paper in purse or wallet
5. Sticky on back of security badge
I use roboform it can generate a password like that and store it. You can also have your roboform on a thumbdrive.
Is there even any evidence that
a) this improves security (given the post-it note problem)
b) the productivty lost isnt more expensive than the actual security risk?
c) it isn't cheaper to use a 'key' on a usb thumbdrive. Possibly combined with a simpler password policy, think of your savings card for eftpos and automatic teller machines - probable combined with a 4 or more digit PIN - whatever you business is your bank is probably the more attractive target - yet cards an pins seem to be a mostly usable solution. It's not like the any of this stuff is expensive?
s.
Do what I do ...use pwgen to create passwords ... after 10 tries you get one which looks like a word is easy to remember and follows the above guideline.
The resistance to using strong, periodically changing passwords is simply astounding, especially with regard to a site handling payroll. What that suggests is a mixture of laziness, impatience, and myopia.
There's a huge difference between reasonably safe passwords (such as those described at ADP), and those which might meet a realistic definition of the abused term "Draconian". A Draconian policy would require long passwords selected from the full 256 character ASCII set, with no repetition. The short, easily dealt with, versions in place at the likes of ADP are meant as a compromise between very safe (though truly Draconian) and the easily breakable crap most users will choose if they can get away with it.
In today's world, the use of good passwords can almost be considered a Darwin test. Good passwords are a survival tool. The sort of password requirements whined about in thread are put in place to protect both users and the environments they log into. Can you say "identity theft"? Can you say "corporate break in"?
I'm stunned at how many people seem willing to admit (or worse yet, brag about) how calcified they've let their brains become with regard to the processes involved in dealing with safe passwords. Fortunately, for those who are unwilling or unable to remember good passwords... there are excellent utilities available to make remembering them unnecessary. Password Safe is one example. Store the password once, then just copy and paste when you need to log in.
Get some perspective, folks. Or at the very least... a sense of self-preservation.
Our policy was just changed to mandate a minimum of FIFTEEN characters in addition to most of the other restrictions outlined on this post. This post provided some catharsis.
And PSweeney, either you missed the point or you're an SA who mandates policies like this yourself. My issue is not that the password policy is annoying, though I do feel that way. It's more like removing your shoes at the airport -- it doesn't necessarily make you safer, but at least the guys in security CAN SAY they're doing something to protect you.
The points have all been made, but I'll reiterate:
1) The SAs who implement policies like this need to remember who they're protecting. Most people don't have the capacity or interest in remembering an insanely complex password, especially if it changes every 30 days. In Windows the default "change reminder prompt" is 14 days before it's due to be changed, so some users change it every 16 days just to avoid the hassle. Changing something so unmemorable every 2 weeks will require most people to jot it down and stick it in a drawer. Call them "calcified" or whatever you will, but that's the simple truth. The more restrictive you are, the more users will adopt counter-measures to simplify their work day.
2) How does mandating 2+ numeric/special/etc characters make my password safer? The total number of password permutations is actually smaller.
the local electric company is almost as bad - they reject my user name and password and city of birth when trying to sign in to pay the bill but if I go direct to their home site and use the same user name and password it accepts them and in my account profile shows all the information is correct. I'm to the point that if anyone can steal my identity that is okay with me if they will only give me say a 10 percent cut
I've given you my damn password a dozen times. This is getting silly. Now let me have my mail and get off the screen.
I literally weep when I have to deal with ADP ipay. It invariable takes at least 20 e-mails to the IT people, HR, and ipay before I can get on. THEY SUCK!!! You have exactly one chance to log on, and, big huge surprise, it never works. Bahhhhhhhhh.
ARGH! I'm riddled with hatred!
I just KEEP having to come up with new passwords for every different fecking site and their specific requirements. WHY CAN'T THERE BE AN AGREED FORMAT!?
OR
There could be a little note when you try to log in saying: Dear user, we noticed that you couldn't log in... it could be because our ridiculous system required this that and the other of your password. This information will probably help to decipher what you ended up using.
It drives me nuts.... I am forced to either write them down, or use an undsecure password so I can remember it. There is no way I can remember complicated, different passwords to my usual password is secure enough.